A few nice machined components China china images I found:
The Sportsmanship of Cyber-warfare …item 2.. Gauss, a new “cyber-espionage toolkit” (August 9, 2012 11:08 AM PDT) …item 3.. New U.S. intelligence report raises urgency over Iran’s nuclear program (Aug.09, 2012)
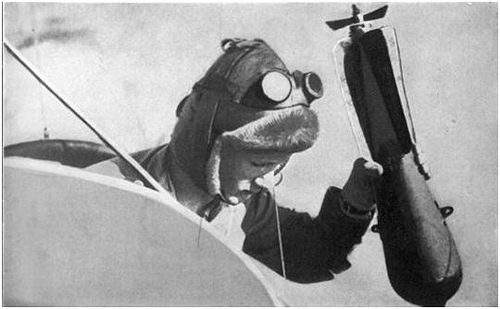
Image by marsmet545
So far, Gauss has swiped data from the Bank of Beirut, EBLF, BlomBank, ByblosBank, FransaBank and Credit Libanais. Citibank and PayPal users are also targeted.
Why Gauss? The malware’s main module was named after German mathematician Johann Carl Friedrich Gauss. Other components are also named after well-known mathematicians.
.
……..*****All images are copyrighted by their respective authors ……..
.
When it comes to protecting a nation, cries of “that’s unfair” or “un-sporting” should be relegated to the “whatever” bucket.
Any nation’s military, counter-intelligence organization, or other agency tasked with protecting its citizens would be catastrophically failing in their obligations if they’re not already actively pursuing new tools and tactics for the cyber-realm.
Granted, just like the military use of aircraft in WW1 opened a Pandora’s box of armed conflict that changed the world forever, ever since the first byte’s traversed the first network we’ve been building towards the state we’re in.
– Gunter Ollmann, VP Research
.
……………………………………………………………………………………………………………………………………………………………………..
.
…..item 1)…. DAMBALLA … blog.damballa.com … THE DAY BEFORE ZERO …
An Ongoing Conversation About Advanced Threats …
Posts Tagged ‘cyberwar’
The Sportsmanship of Cyber-warfare
Wednesday, June 27th, 2012
blog.damballa.com/?tag=cyberwar
As a bit of a history buff I can’t avoid a slight tingling of déjà vu every time I read some new story commenting upon the ethics, morality and legality of cyber-warfare/cyber-espionage/cyberwar/cyber-attack/cyber-whatever. All this rhetoric about Stuxnet, Flame, and other nation-state cyber-attack tools, combined with the parade of newly acknowledged cyber-warfare capabilities and units within the armed services of countries around the globe, brings to the fore so many parallels
.
………………………….
img code photo … The Sportsmanship of Cyber-warfare
blog.damballa.com/wp-content/uploads/2012/06/062712_1930_…
………………………….
.
with the discussions about the (then) new-fangled use of flying-machines within the military in the run-up to WWI.
Call me a cynic if you will, but when the parallels in history are so evident, we’d be crazy to ignore them.
The media light that has been cast upon the (successful) deployment of cyber-weapons recently has many people in a tail-spin – reflecting incredulity and disbelief that such weapons exist, let alone have already been employed by military forces. Now, as people begin to understand that such tools and tactics have been fielded by nation-states for many years prior to these most recent public exposures, reactions run from calls for regulation through to global moratoriums on their use. Roll the clock back 100 years and you’ll have encountered pretty much the same reaction to the unsporting use of flying-machines as weapons of war.
That said, military minds have always sought new technologies to gain the upper-hand on and off the battlefield. Take for example Captain Bertram Dickenson’s statement to the 1911 Technical Sub-Committee for Imperial Defence (TSID) who were charged with considering the role of aeroplanes in future military operations:
“In case of a European war, between two countries, both sides would be equipped with large corps of aeroplanes, each trying to obtain information on the other… the efforts which each would exert in order to hinder or prevent the enemy from obtaining information… would lead to the inevitable result of a war in the air, for the supremacy of the air, by armed aeroplanes against each other. This fight for the supremacy of the air in future wars will be of the greatest importance…”
A century later, substitute “cyber-warriors” for aeroplanes and “Internet” for air, and you’d be hard-pressed to tell the difference from what you’re seeing in the news today.
Just as the prospect of a bomb falling from the hands of an aviator hanging out the cockpit of a zeppelin or biplane fundamentally changed the design of walled fortifications and led to the development of anti-aircraft weaponry, new approaches to securing the cyber-frontier are needed and underway. Then, as now, it wasn’t until civilians were alerted to (or encountered first-hand) the reality of the new machines of war, did an appreciation of these fundamental changes become apparent.
But there are a number of other parallels to WWI (and the birth of aerial warfare) and where cyber-warfare is today that I think are interesting too.
Take for example how the aviators of the day thought of themselves as being different and completely apart from the other war-fighters around them. The camaraderie of the pilots who, after spending their day trying to shoot-down their counterparts, were only too happy to have breakfast, and exchange stories over a few stiff drinks with the downed pilots of the other side is legendary. I’m not sure if it was mutual respect, or a sharing of a common heritage that others around them couldn’t understand, but the net result was that that first-breed of military aviator found more in common with their counterparts than with their own side.
.
…………………………..
img code photo … WW1 Aviators
blog.damballa.com/wp-content/uploads/2012/06/062712_1930_…
…………………………..
.
Today, I think you’ll likely encounter the equivalent social scene as introverted computer geeks who, by way of day-job, develop the tools that target and infiltrate foreign installations for their country, yet attend the same security conferences and reveal their latest evasion tactic or privilege escalation technique over a cold beer with one-another. Whether it’s because the skill-sets are so specialized, or that the path each cyber-warrior had to take in order to acquire those skills was so influential upon their world outlook, many of the people I’ve encountered that I would identify as being capable of truly conducting warfare within the cyber-realm share more in common with their counterparts than they do with those tasking them.
When it comes to protecting a nation, cries of “that’s unfair” or “un-sporting” should be relegated to the “whatever” bucket. Any nation’s military, counter-intelligence organization, or other agency tasked with protecting its citizens would be catastrophically failing in their obligations if they’re not already actively pursuing new tools and tactics for the cyber-realm. Granted, just like the military use of aircraft in WW1 opened a Pandora’s box of armed conflict that changed the world forever, ever since the first byte’s traversed the first network we’ve been building towards the state we’re in.
The fact that a small handful of clandestine, weaponized cyber-arms have materialized within the public realm doesn’t necessarily represent a newly opened Pandora’s box – instead it reflects merely one of the evils from a box that was opened at the time the Internet was born.
– Gunter Ollmann, VP Research
Tags: cyberwar, Flame, stuxnet
Posted in Industry Commentary, Threat Research | No Comments »
.
.
.
Chinese Hackers and Cyber Realpolitik
Friday, December 16th, 2011
For many people the comments made by Michael Hayden, Former Director of the Central Intelligence Agency, at this week’s Black Hat Technical Security Conference in Abu Dhabi may have been unsettling as he commented upon the state of Chinese cyber espionage.
I appreciate the candor of his observations and the distinction he made between state-level motivations. In particular, his comment “We steal secrets, you bet. But we steal secrets that are essential for American security and safety. We don’t steal secrets for American commerce, for American profit. There are many other countries in the world that do not so self limit.”
Perhaps I grew up reading too many spy stories or watched one-too-many James Bond movies, but I’ve always considered one of the functions of government is to run clandestine operations and uncover threats to their citizens and their economic wellbeing. The fact that Cyber is a significant and fruitful espionage vector shouldn’t really be surprising. Granted, it’s not as visual as digging a 1476 foot long tunnel under Soviet Berlin during the Cold War (see The Berlin Tunnel Operation GOLD (U.S.) Operation STOPWATCH (U.K.)) or as explosive as the French infiltration and eventual destruction of the Greenpeace Rainbow Warrior in New Zealand, but in today’s electronic society cyber espionage is a necessary tool.
Personally, I think you’d struggle to find a country or government anywhere around the world that hasn’t invested resources in building out their cyber espionage capabilities in recent years. It’s a tool of modern statecraft and policing.
While the media tends to focus upon the term “cyber warfare” and its many faceted security and safety ramifications, I think that we often fail to divorce a governments need (or even expectation) to conduct espionage and what would logically be covered by the articles (and declaration) of war. Granted it all gets a bit fuzzy – just look at the history of the “Cold War”. Perhaps a more appropriate name for the current situation and tensions would be “Cyber Realpolitik“.
China is often depicted as the bogeyman – rightly or wrongly – when it comes to cyber espionage. We increasingly find ourselves drawn into a debate of whether attacks which are instigated or traced back to the country are state-sponsored, state-endorsed, socially acceptable, or merely the patriotic duty of appropriately skilled citizens. The fact of the matter though is that there’s a disproportionate volume of cyber-attacks and infiltration attempts coming from China, targeting North American and European commercial institutions. You may argue that this is an artifact of China’s population but, if that was the case, wouldn’t India feature more highly then? India is more populous and arguably has a better developed education system in the field of information technology and software development – and yet they are rarely seen on the totem pole of threat instigators.
Michael Hayden alludes that China (and other countries) is not opposed to using cyber espionage for commercial advancement and profit, and based upon past observations, I would tend to agree with that conclusion. That said though, I don’t think that any country is immune to the temptation. Given the hoopla of the recent U.S. congressional insider trading fiasco and French presidential corruption, I’m not sure that “self limit” approaches work in all cases.
Cyber Realpolitik is the world we find ourselves living in and cyber espionage is arguably the latest tool in a government’s clandestine toolkit. We could consume a lot of time debating the ethics and outcomes of modern espionage campaigns but, at the end of the day, it’s a facet of international politics and governmental needs that have existed for millennium. For those commercial entities being subjected to the cyber campaigns directed at them by foreign governments, I don’t believe this threat will be going away anytime in the foreseeable future. Perhaps the noise surrounding the attacks may disappear, but that may just reflect an increase in stealthiness.
– Gunter Ollmann, VP Research.
Tags: APT, China, CIA, cyber espionage, cyberwar, malware
Posted in Industry Commentary, Threat Research | No Comments »
.
.
.
.
…………………………………………………………………………………………………………………………………………………………………….
.
…..item 2)…. CNET News … news.cnet.com … CNET News Security & Privacy
With Gauss tool, cyberspying moves beyond Stuxnet, Flame
Kaspersky Lab finds Gauss, a spying malware that collects financial information and resembles Flame. Components are named after famous mathematicians.
by Larry Dignan … August 9, 2012 11:08 AM PDT
news.cnet.com/8301-1009_3-57490216-83/with-gauss-tool-cyb…
Gauss, a new "cyber-espionage toolkit," has emerged in the Middle East and is capable of stealing sensitive data such as browser passwords, online banking accounts, cookies, and system configurations, according to Kaspersky Lab. Gauss appears to have come from the same nation-state factories that produced Stuxnet.
According to Kaspersky, Gauss has unique characteristics relative to other malware. Kaspersky said it found Gauss following the discovery of Flame. The International Telecommunications Union has started an effort to identify emerging cyberthreats and mitigate them before they spread.
In a nutshell, Gauss launched around September 2011 and was discovered in June. Gauss, which resembles Flame, had its command and control infrastructure shut down in July, but the malware is dormant waiting for servers to become active. Kaspersky noted in an FAQ:
There is enough evidence that this is closely related to Flame and Stuxnet, which are nation-state sponsored attacks. We have evidence that Gauss was created by the same "factory" (or factories) that produced Stuxnet, Duqu and Flame.
.
………………………………
img code photo … The Relationship of Stuxnet, Duqu, Flame and Gauss
cdn-static.zdnet.com/i/story/70/00/002405/kaspersky5.png
………………………………
.
Among Gauss’ key features:
…Gauss collects data on machines and sends it to attackers. This data includes network interface information, computer drive details and BIOS characteristics.
…The malware can infect USB thumb drives using the vulnerabilities found in Stuxnet and Flame.
…Gauss can disinfect drives under certain circumstances and then uses removable media to store collected data in a hidden file.
…The malware also installs a special font called Palida Narrow.
Since May 2012, Gauss has infected more than 2,500 machines, mostly in the U.S. Kaspersky said that the total number of Gauss victims is likely to be in the "tens of thousands." That number is lower than Stuxnet, but higher than Flame and Duqu attacks.
.
……………………….
img code photo … Incidents
cdn-static.zdnet.com/i/story/70/00/002405/kaspersky2.png
……………………….
.
So far, Gauss has swiped data from the Bank of Beirut, EBLF, BlomBank, ByblosBank, FransaBank and Credit Libanais. Citibank and PayPal users are also targeted.
Why Gauss? The malware’s main module was named after German mathematician Johann Carl Friedrich Gauss. Other components are also named after well-known mathematicians.
A few key slides from Kaspersky’s Gauss report:
.
……………………………
img code photo … Unique users
cdn-static.zdnet.com/i/story/70/00/002405/kaspersky1.png
……………………………
.
This story was first published as "Meet Gauss: The latest cyber-espionage tool" on ZDNet’s Between the Lines.
Topics:Cybercrime, Security, Vulnerabilities and attacks Tags:cyber-espionage, Kaspersky Lab, Gauss, malware
.
.
………………………………………………………………………………………………………………………………………………………………………
.
…..item 3)…. HAARETZ … www.haaretz.com/news … HomeNewsDiplomacy & Defense
Barak: New U.S. intelligence report raises urgency over Iran’s nuclear program
Defense Minister Ehud Barak confirms Haaretz’s report that Obama recently received an NIE report which shares Israel’s view on Iran’s progress toward nuclear capability; Israel, U.S. positions on Iran now closer, says Barak.
.
………………………
img code photo … Iron Dome battery site in Ashkelon
www.haaretz.com/polopoly_fs/1.455275.1344511493!/image/33…
U.S. Secretary of Defense Leon Panetta and Defense Minister Ehud Barak hold a joint news conference at an Iron Dome battery site in Ashkelon August 1, 2012.
Photo by Reuters
………………………
.
By Barak Ravid | Aug.09, 2012 | 1:03 PM |
www.haaretz.com/news/diplomacy-defense/barak-new-u-s-inte…
Defense Minister Ehud Barak confirmed on Thursday Haaretz’s report that President Barack Obama recently received a new National Intelligence Estimate report on the Iranian nuclear program, which shares Israel’s view that Iran has made significant progress toward military nuclear capability, and said that the report has raised the urgency of the issue.
Speaking on Israel Radio on Thursday morning, Barak said that there is a U.S. intelligence report "being passed around senior offices," and that, as far as Israel knows, this report has brought the U.S. position over Iran closer to the Israeli position, and made the issue more urgent.
For months there has been a basic agreement (between the U.S. and Israel) over what the Iranians are planning to do, and a deep understanding of what is stopping them, the defense minister said in the interview.
Barak also said that Israel will have to make a decision over Iran’s nuclear program. "All the options are still on the table, and when we say this, we mean it," he said.
"There is still no decision, we understand the gravity of the situation, we understand that we do not have all the time in the world to decide. We are facing tough decisions…we will listen to all assessments and comments, and when we have to make decisions, we will make them, and the decision will of course come from the government," he said.
Haaretz reported on Thursday that the National Intelligence Estimate report on Iran was supposed to have been submitted to Obama a few weeks ago, but it was revised to include new and alarming intelligence information about military components of Iran’s nuclear program. Haaretz has learned that the report’s conclusions are quite similar to those drawn by Israel’s intelligence community.
The NIE report contends that Iran has made surprising, notable progress in the research and development of key components of its military nuclear program.
The NIE reports are the most important assessments compiled by the U.S. intelligence community and are submitted to the president and other top governmental officials. This NIE report was compiled by an inter-departmental team headed by director of National Intelligence James Clapper. Its contents articulate the views of American intelligence agencies.
.
.
……………………………………………………………………………………………………………………………………………………………………..
.
.
Steven F. Udvar-Hazy Center: P-40 Warhawk, SR-71 Blackbird, Naval Aircraft Factory N3N seaplane, Space Shuttle Enterprise

Image by Chris Devers
Quoting Smithsonian National Air and Space Museum | Curtiss P-40E Warhawk (Kittyhawk IA):
Whether known as the Warhawk, Tomahawk, or Kittyhawk, the Curtiss P-40 proved to be a successful, versatile fighter during the first half of World War II. The shark-mouthed Tomahawks that Gen. Claire Chennault’s "Flying Tigers" flew in China against the Japanese remain among the most popular airplanes of the war. P-40E pilot Lt. Boyd D. Wagner became the first American ace of World War II when he shot down six Japanese aircraft in the Philippines in mid-December 1941.
Curtiss-Wright built this airplane as Model 87-A3 and delivered it to Canada as a Kittyhawk I in 1941. It served until 1946 in No. 111 Squadron, Royal Canadian Air Force. U.S. Air Force personnel at Andrews Air Force Base restored it in 1975 to represent an aircraft of the 75th Fighter Squadron, 23rd Fighter Group, 14th Air Force.
Donated by the Exchange Club in Memory of Kellis Forbes.
Manufacturer:
Curtiss Aircraft Company
Date:
1939
Country of Origin:
United States of America
Dimensions:
Overall: 330 x 970cm, 2686kg, 1140cm (10ft 9 15/16in. x 31ft 9 7/8in., 5921.6lb., 37ft 4 13/16in.)
Materials:
All-metal, semi-monocoque
Physical Description:
Single engine, single seat, fighter aircraft.
• • • • •
See more photos of this, and the Wikipedia article.
Details, quoting from Smithsonian National Air and Space Museum | Lockheed SR-71 Blackbird:
No reconnaissance aircraft in history has operated globally in more hostile airspace or with such complete impunity than the SR-71, the world’s fastest jet-propelled aircraft. The Blackbird’s performance and operational achievements placed it at the pinnacle of aviation technology developments during the Cold War.
This Blackbird accrued about 2,800 hours of flight time during 24 years of active service with the U.S. Air Force. On its last flight, March 6, 1990, Lt. Col. Ed Yielding and Lt. Col. Joseph Vida set a speed record by flying from Los Angeles to Washington, D.C., in 1 hour, 4 minutes, and 20 seconds, averaging 3,418 kilometers (2,124 miles) per hour. At the flight’s conclusion, they landed at Washington-Dulles International Airport and turned the airplane over to the Smithsonian.
Transferred from the United States Air Force.
Manufacturer:
Lockheed Aircraft Corporation
Designer:
Clarence L. "Kelly" Johnson
Date:
1964
Country of Origin:
United States of America
Dimensions:
Overall: 18ft 5 15/16in. x 55ft 7in. x 107ft 5in., 169998.5lb. (5.638m x 16.942m x 32.741m, 77110.8kg)
Other: 18ft 5 15/16in. x 107ft 5in. x 55ft 7in. (5.638m x 32.741m x 16.942m)
Materials:
Titanium
Physical Description:
Twin-engine, two-seat, supersonic strategic reconnaissance aircraft; airframe constructed largley of titanium and its alloys; vertical tail fins are constructed of a composite (laminated plastic-type material) to reduce radar cross-section; Pratt and Whitney J58 (JT11D-20B) turbojet engines feature large inlet shock cones.
• • • • •
Quoting Smithsonian National Air and Space Museum | Naval Aircraft Factory N3N:
In 1934 the Naval Aircraft Factory in Philadelphia was tasked to manufacture a new primary trainer for the U.S. Navy. Following successful tests, this little biplane trainer was built in both land and seaplane versions. The Navy initially ordered 179 N3N-1 models, and the factory began producing more than 800 N3N-3 models in 1938. U.S. Navy primary flight training schools used N3Ns extensively throughout World War II. A few of the seaplane version were retained for primary training at the U.S. Naval Academy. In 1961 they became the last biplanes retired from U.S. military service.
This N3N-3 was transferred from Cherry Point to Annapolis in 1946, where it served as a seaplane trainer. It was restored and displayed at the Naval Academy Museum before being transferred here.
Transferred from the United States Navy
Manufacturer:
Naval Aircraft Factory
Date:
1941
Country of Origin:
United States of America
Dimensions:
Overall: 10ft 9 15/16in. x 25ft 7 1/16in. x 34ft 1 7/16in., 2090lb. (330 x 780 x 1040cm, 948kg)
Materials:
bolted steel-tube fuselage construction with removable side panels wings, also constructed internally of all metal, covered with fabric like the fuselage and tail.
Physical Description:
Bright yellow bi-plane, hand crank start. Cockpit instrumentation consists of an altimeter, tachometer, airspeed indicator, compass, turn and bank indicator, and a combination fuel and oil temperature and pressure gauge, floats.
• • • • •
See more photos of this, and the Wikipedia article.
Details, quoting from Smithsonian National Air and Space Museum | Space Shuttle Enterprise:
Manufacturer:
Rockwell International Corporation
Country of Origin:
United States of America
Dimensions:
Overall: 57 ft. tall x 122 ft. long x 78 ft. wing span, 150,000 lb.
(1737.36 x 3718.57 x 2377.44cm, 68039.6kg)
Materials:
Aluminum airframe and body with some fiberglass features; payload bay doors are graphite epoxy composite; thermal tiles are simulated (polyurethane foam) except for test samples of actual tiles and thermal blankets.
The first Space Shuttle orbiter, "Enterprise," is a full-scale test vehicle used for flights in the atmosphere and tests on the ground; it is not equipped for spaceflight. Although the airframe and flight control elements are like those of the Shuttles flown in space, this vehicle has no propulsion system and only simulated thermal tiles because these features were not needed for atmospheric and ground tests. "Enterprise" was rolled out at Rockwell International’s assembly facility in Palmdale, California, in 1976. In 1977, it entered service for a nine-month-long approach-and-landing test flight program. Thereafter it was used for vibration tests and fit checks at NASA centers, and it also appeared in the 1983 Paris Air Show and the 1984 World’s Fair in New Orleans. In 1985, NASA transferred "Enterprise" to the Smithsonian Institution’s National Air and Space Museum.
Transferred from National Aeronautics and Space Administration